Account & Network Integrity Inspection – mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, Njgcrby
Account & Network Integrity Inspection presents a structured framework for evaluating trust across identities, sessions, and channels. It emphasizes proactive monitoring, real-time anomaly detection, and strict policy enforcement to prevent breaches. The approach ties governance, credentials, and access controls to continuous vigilance, ensuring resilient connections without compromising usability. Goals are clear: sustain secure collaboration among vetted endpoints while maintaining operational continuity. The implementation path is precise, but gaps remain that demand careful consideration and further refinement.
What Is Account & Network Integrity Inspection?
Account & Network Integrity Inspection is a systematic process designed to verify and validate the trustworthiness of digital accounts and the networks they operate within. It assesses governance, credentials, and access controls to ensure reliability.
Proactive Monitoring That Stops Breaches Before They Start
Proactive monitoring transforms integrity enforcement from reactive incident response into continuous defense, leveraging real-time signals to detect anomalies and neutralize threats before they manifest as breaches.
The approach enacts security governance with rigorous threat modeling, ensuring resilient user authentication, disciplined network segmentation, and proactive risk reduction.
This disciplined stance empowers freedom by preventing disruption and safeguarding trusted operations.
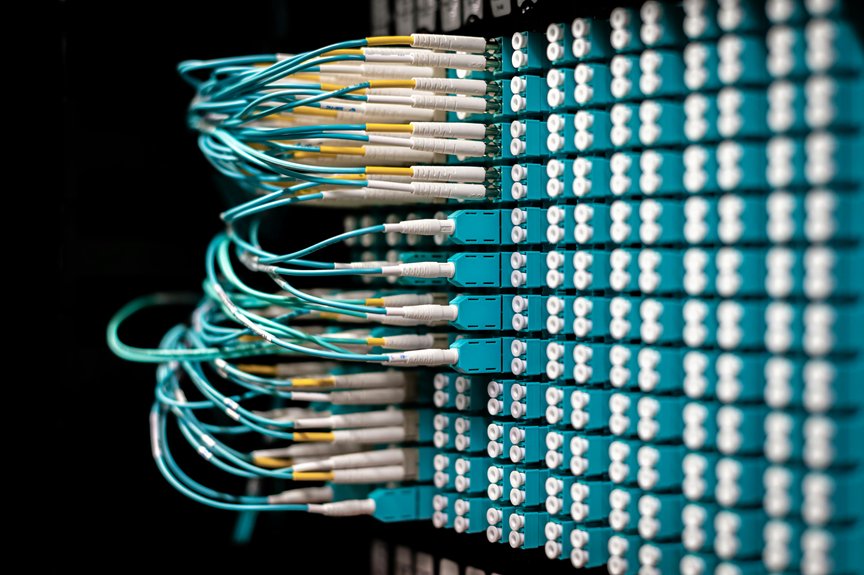
Verification and Anomaly Detection for Trusted Connections
The method emphasizes proactive scrutiny, consistent usability audit, and strict policy alignment, identifying irregularities without disruption.
Results guide disciplined access decisions, reinforcing resilience while preserving freedom, transparency, and uninterrupted collaboration across trusted endpoints.
Practical Steps to Implement Holistic Integrity in Your Network
A pragmatic framework for holistic integrity in a network begins by consolidating trust across identity, session, and channel layers, ensuring that credential validity, session continuity, and data path stability are continuously verifiable.
Implement practical steps: enforce account hygiene, define clear trust boundaries, deploy continuous network monitoring, and configure timely anomaly signaling to preserve resilient, freedom-embracing operational integrity.
Conclusion
In the kingdom of network passages, a vigilant harbor master stands, charting every tide between trusted ports. The system acts as a steadfast gatekeeper, weighing each beacon and badge with unerring precision. Storms of breach chatter are silenced by proactive vigilance, while sanctioned currents flow unimpeded. As lines of code tighten like rope and compass, fidelity becomes policy, and collaboration survives the voyage—secure, resilient, and unswervingly aligned with the truth of governance.




