Check and Validate Call Data Entries – 2816720764, 3167685288, 3175109096, 3214050404, 3348310681, 3383281589, 3462149844, 3501022686, 3509314076, 3522334406
This discussion centers on the rigorous check and validation of call data entries for the listed numbers. It focuses on aligning timestamps, caller and recipient IDs, duration, outcome, and metadata against a single source of truth. The aim is precise matching, reproducible scripts, and audit-ready documentation to support traceability, anomaly detection, and governance. Discrepancies will be flagged for targeted investigation, preserving a complete audit trail and enabling repeatable reconciliation workflows to prevent recurrence.
What Are Accurate Call Data Entries and Why They Matter
Accurate call data entries are precise, complete records of each call’s key attributes, including timestamps, caller and recipient IDs, duration, outcome, and any relevant metadata.
In this context, accurate entries support accountability and traceability.
The emphasis is on structured recording, uniform formats, and verifiable sources.
Data validation ensures consistency, detect anomalies, and uphold integrity across monitoring systems and audits.
How to Source-Of-Truth Validate Each Entry (2816720764, 3167685288, 3175109096, 3214050404, 3348310681, 3383281589, 3462149844, 3501022686, 3509314076, 3522334406)
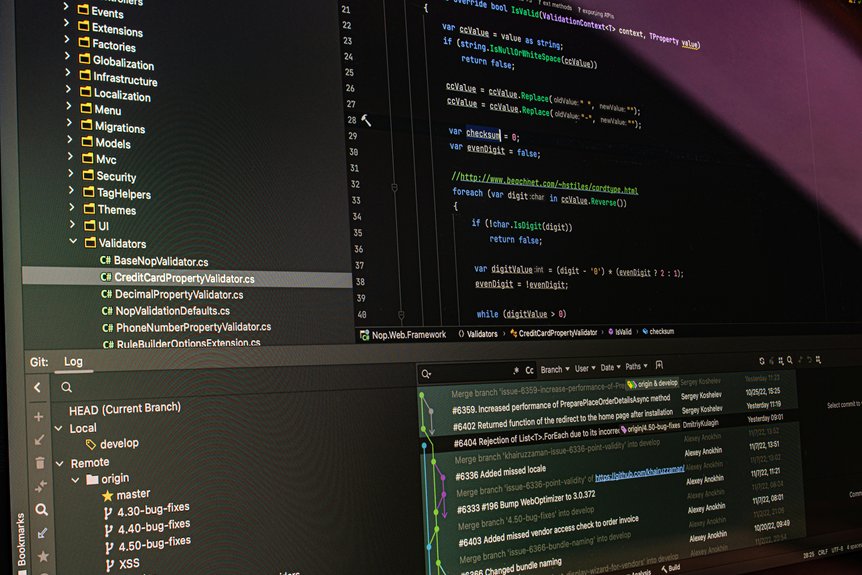
To establish a reliable source-of-truth for each call data entry, the process begins with mapping every required field to a single, authoritative record, ensuring that timestamps, participant IDs, duration, outcomes, and metadata align across systems.
The source of truth is established through a disciplined validation process, emphasizing traceability, auditability, and consistent data governance without ambiguity.
Practical Reconciliation Steps and Anomaly Detection
Practical reconciliation steps begin with a disciplined, source-aligned comparison of critical fields across systems, focusing on timestamps, participant identifiers, call duration, outcomes, and metadata.
The methodology emphasizes precise matching criteria, scripted validation checks, and audit-ready documentation.
Anomaly detection identifies outliers, gaps, or mismatches, guiding targeted investigations while preserving traceability and operational freedom through transparent, repeatable reconciliation workflows.
Establishing Audit Trails and Preventive Controls
Establishing controls mitigates risk by ensuring consistent data handling, timely anomaly flagging, and policy compliance. Methodical recordkeeping reinforces accountability, while governance transparency sustains reliability and operational freedom within structured, disciplined procedures.
Conclusion
In the realm of call data, a ship’s log is kept with exact bearings: timestamps, parties, duration, and outcomes must align with a single, authoritative chart. Each entry is cross-checked against the source-of-truth, discrepancies flagged for targeted investigation, and an auditable trail preserved to ensure governance and repeatability. Through scripted validation, anomaly detection, and disciplined reconciliation, the data remains trustworthy, traceable, and ready for governance-driven decision-making.