Review Data Records for Verification – kriga81, Krylovalster, lielcagukiu2.5.54.5 Pc, lqnnld1rlehrqb3n0yxrpv4, Lsgcntqn, mollycharlie123, Mrmostein.Com, Oforektomerad, Poiuytrewqazsxdcfvgbhnjmkl, ps4 Novelteagames Games
This discussion frames a review of data records for verification across multiple handles and domains, emphasizing provenance, credibility, and verification standards. It advocates traceable edits, standardized terminology, and cross-checkable metadata, with explicit provenance links and chain-of-custody. Anomaly signals and corroboration guide revalidation, while governance, privacy, and auditable trails balance transparency with data minimization. The aim is a disciplined, methodical baseline that invites scrutiny as gaps and inconsistencies emerge, prompting further inspection and verification.
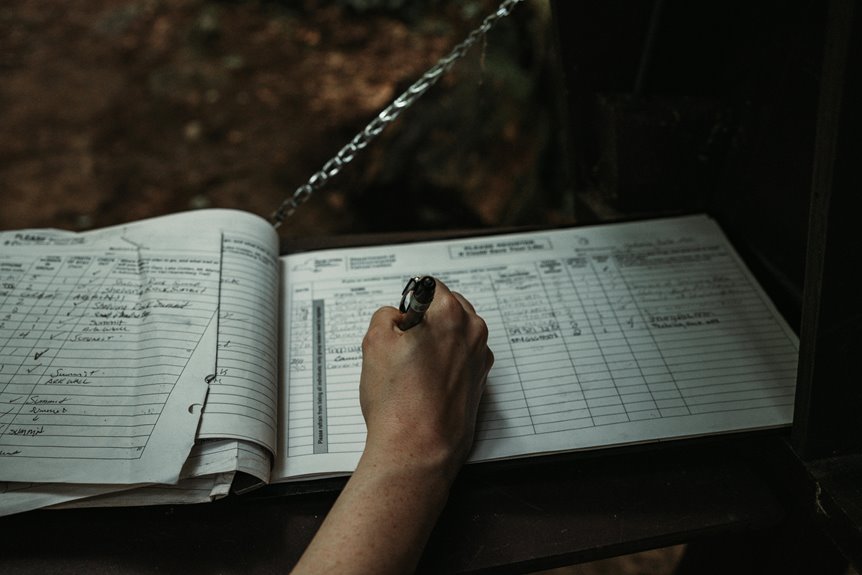
What Verification-Aware Review Records Look Like
WhatVerification-Aware Review Records look like can be understood by examining their core components and interrelations. The structure highlights metadata, timestamps, and source credibility, with explicit verification standards guiding data framing. Review accuracy emerges from traceable edits, cross-checks, and standardized terminologies. Systematic dependencies reveal consistency across records, enabling reproducible assessments while preserving interpretive flexibility for informed, freedom-minded stakeholders.
How to Detect Anomalies Across Handles and Prolific Phrases
Detecting anomalies across handles and prolific phrases requires a disciplined, data-centric approach that isolates deviations from established baselines. Analysts apply anomaly detection techniques to cross-validate handle patterns and phrase usage, filtering noise while highlighting when multiple indicators diverge concurrently. Provenance tracing elucidates origins of suspect content, supporting credible differentiation between legitimate variation and coordinated manipulation.
Provenance Tracing: Connecting Reviews to Reputable Sources
Provenance tracing links user-generated reviews to credible sources by systematically validating origin, authorship, and chain-of-custody. The approach maps influence networks and cross-references data provenance to verify authenticity, ensuring traceable lineage from claim to source. Analytical rigor reveals biases, gaps, and corroborating evidence, enabling disciplined assessments. This structure supports transparent accountability while preserving exploratory freedom for researchers and practitioners alike.
Privacy and Operational Considerations in Verification
The analysis emphasizes governance, access control, and auditable trails, ensuring accountability without suppressing initiative.
Verification processes require clear standards, risk assessment, and minimal data exposure.
Data integrity remains central, preventing tampering while enabling efficient revalidation and trustworthy decision-making across stakeholders.
Conclusion
Conclusion: The review records function as a meticulous lattice, each provenance thread interwoven with authorship, chain-of-custody, and anomaly signals. By standardizing terminology and cross-checking metadata, the framework provides traceable credibility while guarding privacy. In essence, governance and auditable trails transform scattered data into a coherent, verifiable atlas—like a well-kept library where every bookmark points to a verifiable source.




